Key Takeaways
- Secure multi-account automation means controlled, separated, and reviewable automation across multiple account workflows.
- Cloud phones help when each account lane needs its own device state, route policy, access boundary, and recovery path.
- The goal is not absolute safety. The goal is fewer unknowns, cleaner handoff, and stronger operational control.
- Teams should connect automation to device isolation, proxy rules, role control, logs, and pilot metrics.
- Start with one workflow and prove recovery before scaling to more accounts or more devices.
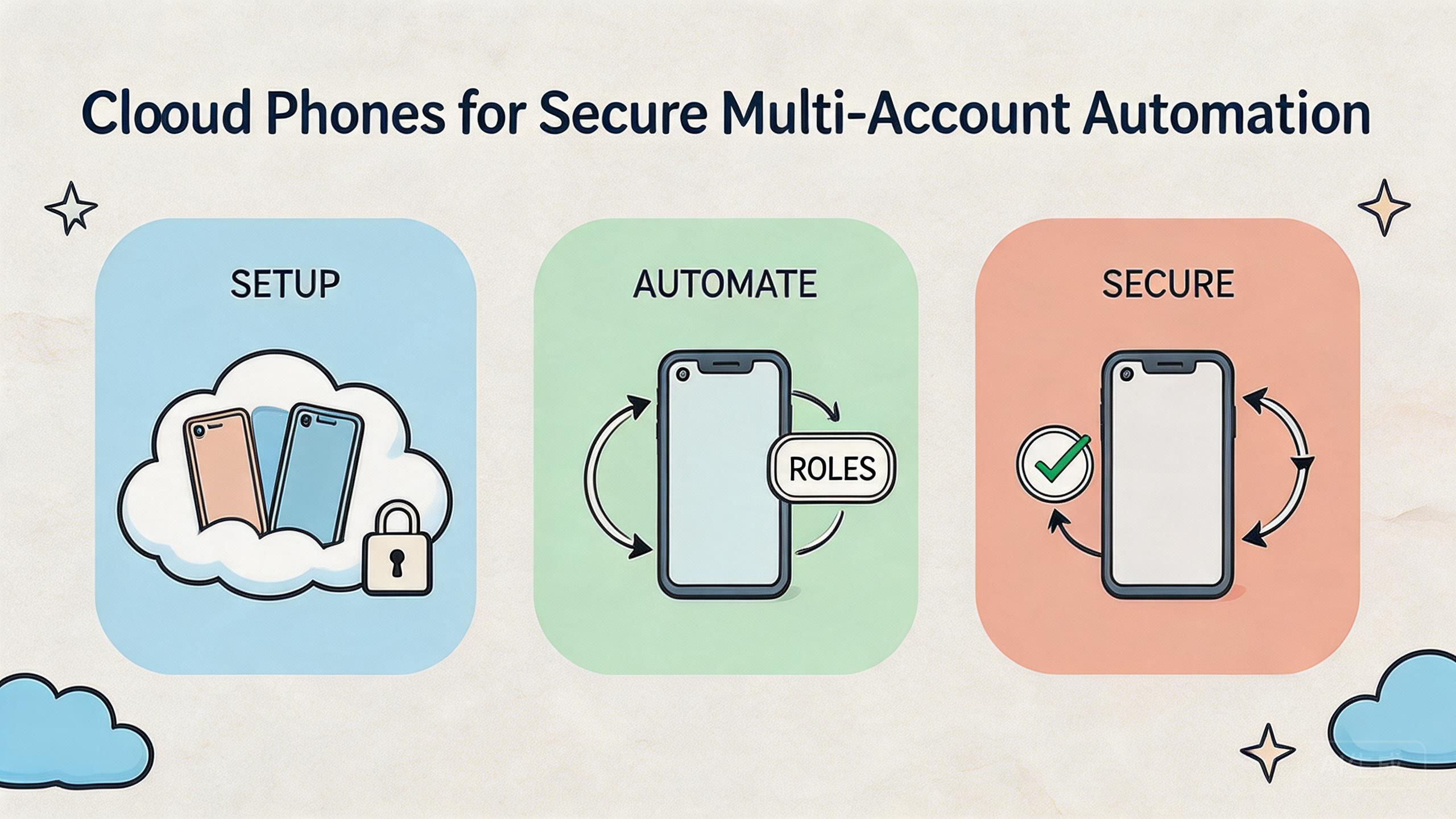
Secure multi-account automation is the controlled use of automation across several account workflows with clear separation, access rules, logs, and recovery steps. Remote Android pools support this model by giving teams devices that can be assigned, isolated, reviewed, and reset.
The direct answer is practical. A cloud phone can help secure multi-account automation when the team needs repeatable mobile execution without mixing device state or account lanes. It does not remove platform rules, policy duties, or operator risk. It gives the team a better control layer.
This distinction matters. Many teams focus on automation speed first. They want more tasks, more accounts, and more devices. The stronger order is different: define the workflow, separate the lanes, control access, stabilize routing, track results, and then automate repeat steps.
MoiMobi treats cloud phones as execution infrastructure, not only remote screens. The cloud phone layer should work with device isolation, proxy network, multi-account management, and mobile automation.
Google Search Central’s helpful content guidance says useful content should help people complete real tasks, not repeat surface-level claims (Google Search Central). A useful automation setup should do the same. It should help a team run, review, and recover real workflows.
The Core Idea Behind Secure Multi-Account Automation
The operating model starts with separation. Every account workflow should have a known device lane, known route policy, known user role, and known recovery step. Automation should operate inside that lane instead of crossing unclear boundaries.
The word secure should be used carefully. In this context, it does not mean a magic shield. It means the team reduces avoidable operational risk by making account work easier to separate, track, and recover.
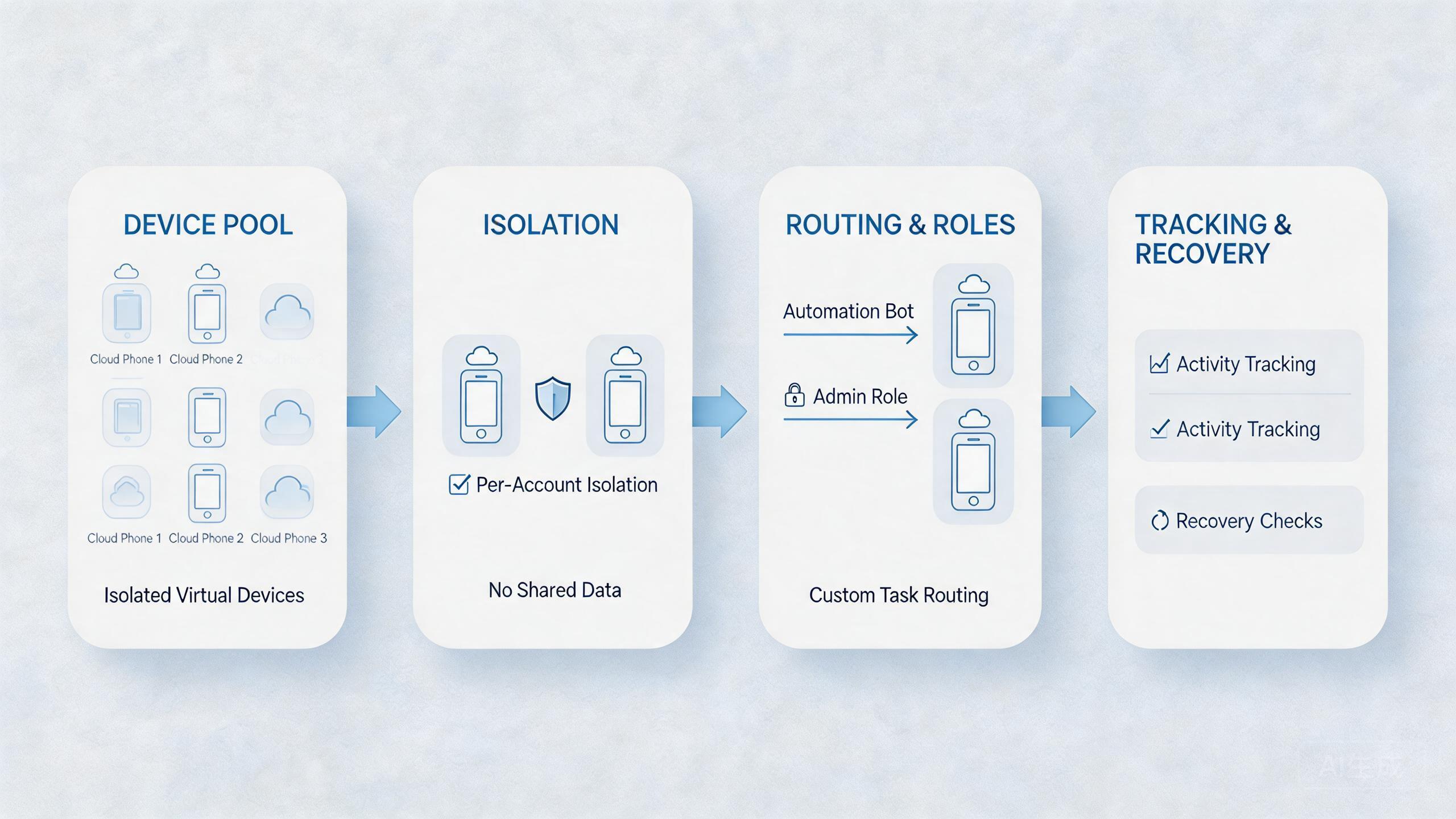
Remote device pools help because they can be grouped by job. One pool may support social account checks. Another may support ecommerce review. A third may support QA or support reproduction. The point is that each pool has a purpose.
The basic system has four parts:
| Layer | Purpose | What to review |
|---|---|---|
| Account lane | Defines which accounts belong to one workflow | Is ownership clear? |
| Device pool | Provides cloud phones for that lane | Is device state clean before reuse? |
| Routing policy | Connects the lane to a known network path | Can the route be explained? |
| Automation rule | Controls what scripts or workflows may do | Are actions logged and limited? |
This model keeps automation from becoming an uncontrolled batch process. The team knows which lane ran, which device was used, which route applied, and what result followed. That is the foundation for review.
Why Teams Search for This Topic
Teams search for secure multi-account automation when manual account work becomes too slow or hard to coordinate. One person can manage a few tasks with notes and memory. A team running many mobile workflows needs more structure.
The common misunderstanding is that automation alone creates control. It does not. Automation repeats actions. It can also repeat mistakes. The control comes from separation, permissions, logs, and recovery rules.
Remote teams also need shared visibility. A cloud phone pool can make account work easier to assign and review. Instead of asking who has a physical phone, the team can ask which device lane owns the task and whether the lane is ready.
Routing is another reason. Account workflows often need explainable network behavior. A route that changes without notes can make failures hard to diagnose. Pairing account lanes with a known proxy network policy improves review quality.
Teams also want cleaner handoff. An operator may start a workflow, a reviewer may inspect it, and an admin may reset the device. That process breaks when all three people rely on private notes. Remote phone infrastructure can make state and ownership easier to see.
Search intent usually includes four questions:
- How do we separate account work?
- How do we automate without losing review control?
- How do we know which device and route ran a task?
- How do we recover when a run fails?
The strongest answer is not “add more automation.” The strongest answer is “build a controlled lane, then automate the repeat parts.” Google Play’s policy resources are a reminder that platform rules still matter regardless of infrastructure choices (Google Play Policy Center).
Who Benefits Most and In What Situations
This approach fits teams that already understand their account workflows. Operators should know what must repeat, what needs review, and what should remain manual. Clear work becomes easier to automate. Unclear work becomes harder to trust.
Agencies may benefit when they manage account tasks for several clients or campaigns. They need boundaries between lanes. A cloud phone pool can keep client or workflow state easier to separate when the team names and reviews each lane.
Ecommerce teams may use the model for store checks, app checks, support review, or account operations. The value comes from device state clarity. Operators should know which cloud phone belongs to which workflow and what status it carries.
Social operations teams need extra caution. A social media marketing workflow may involve content, accounts, platform rules, and review steps. Automation should support checks and handoff, not replace responsible judgment.
Support and QA teams can also use cloud phones for repeat checks. A failed flow may need a known device state, route, and action log. A structured cloud phone lane helps the team reproduce and review issues.
Fit is strongest here:
Repeated account checks, app review, QA smoke paths, support reproduction, pre-run validation, and controlled mobile automation.
Social workflows, ecommerce account work, and growth operations where platform rules and human review still matter.
Undefined workflows, mixed account pools, broad automation without logs, or tasks that require physical device inspection.
The fit boundary is simple. Use cloud phones when separation and remote review improve the workflow. Keep local devices or manual review where physical checks, judgment, or policy review matter more than repetition.
How to Evaluate or Start Using Cloud Phones for Secure Multi-Account Automation
The mistake to avoid is starting with the largest account set. Big launches hide small process flaws. A better pilot starts with one workflow, one owner, one cloud phone pool, and one review loop.
- Choose one account lane. Pick a repeated workflow with a clear owner and clear success criteria.
- Assign a cloud phone pool. Keep devices grouped by workflow so account state does not drift across lanes.
- Set routing rules. Decide which route policy belongs to the lane and when it can change.
- Limit automation actions. List what the automation may do, what requires review, and what is not allowed.
- Separate user roles. Operators, reviewers, and admins should not all have the same control level.
- Log outputs. Store enough detail to show device ID, lane, route, operator, run result, and failure reason.
- Define recovery. Decide when to reset, quarantine, review, or return a device to service.
The highest-risk step is automation scope. A script that can touch every account lane is hard to review. Early automation should handle narrow, visible tasks. Examples include readiness checks, app state checks, status capture, or simple workflow steps.
Pair automation with device isolation. Every account lane should have a clean device boundary. Operators should know when a device is ready, in use, under review, or reset needed.
Review the pilot before expanding. Ask whether another operator can run the same workflow without private notes. A negative answer means the process is not ready for more accounts.
Mistakes That Reduce Results
The first mistake is confusing speed with control. Faster account work can create larger problems when lanes are mixed. A controlled automation lane should reduce ambiguity, not only increase throughput.
The second mistake is using one shared device pool for unrelated workflows. Mixed pools make it hard to know which account state belongs to which task. Separate pools may feel slower at first, but they make review easier.
The third mistake is skipping route documentation. A route change may look small. Later, the team may not know why a workflow result changed. Route notes should be part of the run record.
Another mistake is flat access. If every user can run, review, reset, and change routing, mistakes are harder to trace. Role separation keeps actions more accountable.
Some teams also ignore failed-run handling. A failed automation run can leave app state, account state, or device state unclear. Without a recovery rule, the next operator may inherit a bad lane.
Over-automation is another risk. Not every decision should be scripted. Keep human review where judgment, policy, account context, or exception handling matters. Automation should support repeat steps, not replace all review.
Finally, teams often scale before proof. One successful run is not proof. A workflow should stay stable across users, devices, and days before it expands.
Pilot Rollout, Measurement, and Recovery Checks
A pilot should prove that cloud phones improve the account workflow. The goal is cleaner operations, not just more runs. Measure whether the team can start, run, review, and recover with fewer unknowns.
Track five signals:
| Signal | What to measure | Useful result |
|---|---|---|
| Setup time | Time from assigned task to ready device | Less waiting and fewer setup questions |
| Lane clarity | Whether the account lane is easy to identify | Fewer mixed-state problems |
| Route clarity | Whether the route is known and logged | Faster troubleshooting |
| Handoff quality | Whether a reviewer can understand status | Fewer private notes |
| Recovery time | Time to reset or review a failed device | Faster return to service |
Run the pilot several times before scaling. A single clean run can happen by chance. Repeat runs show whether the lane is reliable. Use the same owner, device pool, route policy, and output format during the test.
Recovery needs a written rule. Decide when a device becomes reusable, when it needs reset, and when it should be quarantined. A vague label like “probably fine” is not enough for team operations.
The review loop should ask:
- Did the correct account lane run?
- Did the correct device pool run?
- Did the expected route apply?
- Did the automation stay inside its allowed actions?
- Did the output explain success or failure?
- Is the device ready for the next run?
This review loop keeps secure multi-account automation grounded in evidence. It also helps leaders decide whether to expand or fix the base workflow first.
Governance Rules for Secure Multi-Account Automation
Governance does not need to be complicated. A small rule set can prevent most avoidable confusion. Everyone should know who owns each lane, who can change automation rules, and who can return devices to service.
Start with naming. Every lane should have a clear name. The name should show the workflow, not a private nickname. For example, “support-review-pool” is easier to understand than “pool-two.”
Next, define ownership. One accountable owner should control each account lane. That owner should approve route changes, automation scope changes, and recovery decisions. Shared responsibility often becomes no responsibility.
Access should match the role:
- Operators run assigned workflows.
- Reviewers inspect results and status.
- Admins manage device pools and routes.
- Technical owners investigate repeated failures.
Logs should stay short and useful. A good run record includes device ID, lane, route class, user, automation version, result, and failure reason. This is enough for most daily reviews.
Weekly cleanup also matters. Remove stale lanes, unused devices, unclear route notes, and old automation rules. Small cleanup keeps the system understandable as the account set grows.
Google’s SEO Starter Guide emphasizes clear structure so users can understand information and take action (Google Search Central SEO Starter Guide). Team operations need the same habit. Clear structure makes action safer and easier to review.
Operating Architecture for Secure Multi-Account Automation
An automation lane needs a small architecture before it needs more volume. The architecture does not need to be complex. It only needs to show where work starts, which device pool runs it, which route applies, and how the result is reviewed.
The first part is the account map. Every account should belong to a named lane. The lane may represent a client, region, campaign, store, app test, or support workflow. The name should be clear enough that a new operator understands the purpose.
The second part is the device map. Each lane should have a cloud phone pool or a clear assignment rule. Device state should not move between unrelated account lanes without review. This keeps app data, session state, and workflow history easier to inspect.
The third part is the route map. Each lane should have a known routing policy. The team should record when a route changes and why. This makes later troubleshooting much faster.
The fourth part is the automation map. Each script or workflow should have a named owner and allowed action list. The output should show which account lane ran, which device was used, what result appeared, and what action is next.
A simple architecture check looks like this:
- Account lane is named.
- Device pool is assigned.
- Route policy is visible.
- Automation action list is limited.
- Result output is readable.
- Recovery owner is named.
- Review status is updated after each run.
This structure helps teams avoid the most common failure: fast execution with unclear state. A slower pilot with clean records is more useful than a large run nobody can explain.
The architecture also helps managers. They can see which lanes are stable, which lanes are failing, and which lanes need reset work. That is more useful than only counting successful automation runs.
Security Review Checklist Before Scaling
A security review checklist should be short enough for daily use. Long review forms often get ignored. The useful version asks whether the lane is separated, whether access is limited, and whether a failed run can be explained.
Start with account scope. The automation should know which accounts belong to the lane and which accounts are outside the lane. A script should not be able to reach unrelated work just because it runs in the same workspace.
Check device scope next. The cloud phone pool should match the account lane. Any device used for another workflow should be marked for review before reuse. A clean label is more useful than a private note.
Review route scope before each larger run. The route should match the lane and should not change without a recorded reason. When routing changes, the run record should show who approved it and why.
Inspect action scope as well. The automation should have an allowed action list. A safe pilot might only check state, collect output, or run a short task. Broader actions should wait until the team can review failures quickly.
Use this pre-scale checklist:
- Account lane is named.
- Device pool matches the lane.
- Route policy is visible.
- Automation actions are limited.
- User role is correct.
- Output is readable.
- Recovery owner is available.
- Failed-run state is not reused.
This review does not promise perfect safety. It creates a repeatable pause before scale. That pause helps teams catch unclear lanes before automation spreads the problem across more accounts.
Frequently Asked Questions
What is secure multi-account automation?
It is controlled automation across several account workflows. The key parts are separation, limited access, logs, routing rules, and recovery.
Do cloud phones make account automation safe?
No tool makes account work automatically safe. Managed remote-device infrastructure can improve control, separation, and review when the workflow is designed carefully.
Why use cloud phones instead of local devices?
Remote device pools help when teams need shared remote access, parallel device pools, handoff, and review visibility. Local devices still fit physical testing.
What should be isolated?
Isolate device state, account lanes, routing policy, user access, and recovery status. Those boundaries make review easier.
Can automation run across many accounts at once?
It can, but broad automation should come after a small pilot. Start with one lane, prove recovery, then expand carefully.
What is the biggest operational risk?
The biggest risk is unclear state. Mixed accounts, unclear routes, broad permissions, and missing logs make failures hard to explain.
How should teams measure success?
Measure setup time, route clarity, handoff quality, failure reasons, and recovery time. These signals show whether the workflow is getting cleaner.
Should every user have automation access?
No. Operators, reviewers, admins, and technical owners need different access levels. Flat access makes mistakes harder to trace.
Conclusion
Controlled multi-account automation should start with control before speed. First, separate account lanes. Second, assign cloud phone pools. Third, define route policy. Fourth, limit automation actions. Fifth, track results and recovery.
Remote Android pools give teams a device layer that can be grouped, reviewed, and reset. They are strongest when paired with device isolation, proxy rules, role control, and clear logs.
The next step is to choose one repeated account workflow and run a narrow pilot. Use one pool, one owner, one route policy, and one recovery rule. Expand carefully when the pilot reduces confusion and improves handoff. Otherwise, fix the operating model before adding more devices or more automation.
Stable multi-account execution comes from clear lanes, not from volume alone. Build the lane first. Automate the repeat parts second. Scale only after the workflow can be reviewed without guessing.