Why Choose Cloud Phones
Considering key factors like compliance, account banning risks, practical operational needs, and platform limitations, cloud phones provide a safer and more authentic operating environment for multi-scenario automation needs.
Automate your APP operations and marketing on cloud phones
Support Instagram / Facebook / YouTube / WhatsApp / Telegram and more, batch and stable
Cloud Phone Cluster & Isolation
Flexible device pool with smart IP & fingerprint isolation.
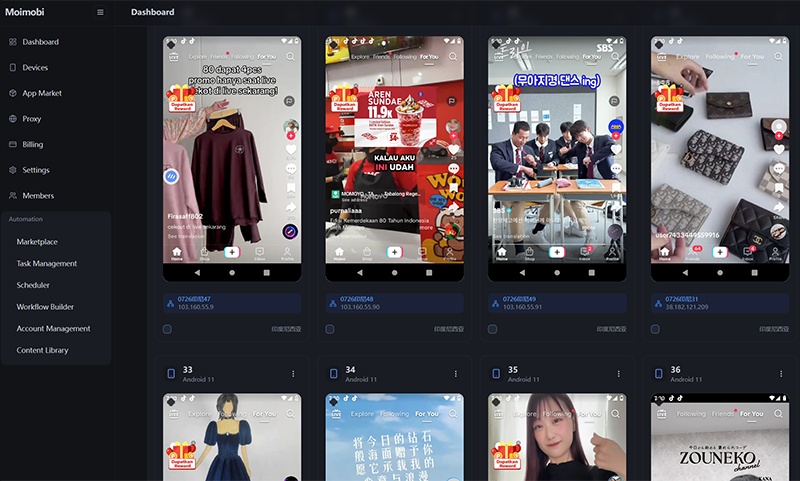
Multi-Platform Support
Supports global social, e-commerce, and ad platforms.
Automated Workflow Orchestration
Automated execution with scheduled/triggered/loop operations, 24/7 automated operations.
- Social media postCancelled by user
- Lead list70% prepared
- Payment remindersent to selected clients
- Payroll managementDue on 2nd july
- Employee Tracking2 days ago
- Campaign launchAssets reviewed
- Content review3 items pending
- Report exportGenerating weekly report
- Social media postCancelled by user
- Lead list70% prepared
- Payment remindersent to selected clients
- Payroll managementDue on 2nd july
- Employee Tracking2 days ago
- Campaign launchAssets reviewed
- Content review3 items pending
- Report exportGenerating weekly report
Marketing & Growth Tools
Automate comments, likes, DMs, and build scalable campaigns.
User Interaction
Instagram, TikTok
Content Publishing
YouTube, Facebook
Customer Service
WhatsApp, Telegram
Social Engagement
Twitter, LinkedIn
Auto Response
Multi-platform
Risk Control & Analytics Dashboard
Account-centric metrics: track total accounts, active rate and risk alerts with real‑time monitoring and exportable reports.
Why Fingerprint Tools & API Platforms Fall Short
Fingerprint Automation Tools
- Low cost, fast switching, suitable for batch account farming and automation
- Easy setup and management for simple automation tasks
- Browser environment + proxy easily detected, once rules updated, mass account bans
- Cannot support mobile app operations (like TikTok video publishing, editing, private messaging)
- Platforms increasingly recognize these behavioral patterns
API-based Platforms (Hootsuite, Buffer)
- Safe, stable, and compliant with platform terms
- Official API integration ensures reliability
- Cannot bypass API permission limitations, cannot simulate real user behavior
- Cannot support real behaviors like 'recommendations, likes, comments, private messages'
- Not suitable for multi-account matrix, AI agent operations, viral marketing and other purposes
Cloud Phones: The Closest to 'Real Human' Operating Environment
Cloud phones are essentially 'always-online Android real device simulation environments' with extremely high 'real user' simulation capabilities from platform recognition perspective:
Real Environment Simulation
Complete IMEI, GPS, SIM status, system language, sensors, user behavior traces - indistinguishable from real devices.
Full App Support
Run complete applications like TikTok, Facebook, Telegram, Instagram with native functionality and user experience.
Advanced Automation
Script integration (ADB + Monkey + Auto-click) for complex automation workflows while maintaining human-like behavior.
Anti-correlation Protection
Combined with proxy + independent fingerprint simulation for multi-account environment isolation and account correlation prevention.
Why Use Cloud Phones
Cross-border Marketing Teams
Segment 1
Need app posting, commenting, interaction, and persona building
Fingerprint tools cannot operate apps
Amazon FACEBOOK E-commerce Sellers
Segment 2
Need real app login (like Amazon Seller, Facebook Shop)
Simulator or API operations face severe banning
AI Virtual Employee Entrepreneurs
Segment 3
Build AI virtual employees for intelligent customer service and marketing automation
Fingerprint tools cannot support complex AI interaction scenarios
AI Marketing SaaS Entrepreneurs
Segment 4
Deploy 'AI virtual humans' for automated interaction
Browser automation cannot support video platforms
App Developers and Test Engineers
Segment 5
Need multi-device compatibility testing, automated testing, performance monitoring
Physical devices are high-cost, complex to manage, poor scalability
Enterprise Application Development Teams
Segment 6
Deploy enterprise apps, remote work, device management and security control
Traditional solutions cannot provide unified device management and security policies
App Testing and Development
Segment 7
Need real device environments for compatibility testing, performance optimization, user experience validation
Physical devices are expensive, complex to manage, unable to quickly scale testing
Cross-border Ad Verification
Segment 8
Verify ad display effectiveness in different regions, anti-fraud detection, ad compliance testing
Traditional methods cannot simulate real geographical locations and device environments
Smart Remote Mobile Office
Segment 9
Remote employee access to enterprise mobile apps, secure mobile office environment, unified device management
Personal devices have high security risks, difficult to implement unified enterprise security policies
Cryptocurrency Airdrop Farming
Segment 10
Multi-account mining, airdrop collection, DeFi protocol interaction, NFT minting
Requires massive real device environments, traditional methods are too costly and easily detected
Ready to Experience the Difference?
Join thousands of businesses who have made the smart choice. Experience the security, freedom, and reliability that only cloud phones can provide.